
Email spoofing poses an escalating risk to your brand’s reputation and can undermine the trustworthiness of your email communications. A practical solution to safeguard your domain is utilizing an SPF generator, which aids in crafting precise Sender Policy Framework records for your DNS. By specifying which mail servers are authorized to send emails for your domain, SPF acts as a barrier against attackers attempting to impersonate your organization.
Employing an SPF generator makes configuring SPF records easier and enhances email authentication as well as deliverability. When effectively combined with protocols such as SPF, DKIM, and DMARC, it enables recipient mail servers to authenticate genuine senders while filtering out potentially fraudulent messages. This approach not only bolsters your email security but also increases the likelihood that your legitimate communications will land in the inbox rather than the spam folder.
Why SPF matters: stopping spoofing, phishing, and improving deliverability
Stop spoofing and phishing
SPF is a foundational control for email security that helps receiving servers verify whether a sending host is authorized to use your domain name. By publishing an accurate SPF record in your DNS, you make it harder for attackers to forge your From address and launch phishing or business email compromise.
When mailbox providers run an SPF record check with their SPF checker, they compare the connecting IP against your listed IPv4 and IPv6 sources, A record and MX record references, and any include directives. A valid SPF record closes easy impersonation paths and supports broader outbound email security and email protection programs.
Lift email deliverability and inbox placement
Accurate SPF policies also boost email deliverability. ISPs and enterprise gateways factor SPF outcomes into sender reputation, spam scoring, and inbox placement decisions. If your SPF record fails or is missing, you’ll see more bounces, quarantine actions, and promotions-tab placements that depress email campaigns.
Using an SPF generator or an SPF record generator reduces configuration drift so your domain name stays aligned with real senders, keeping email verification signals consistent across providers and improving long-term email health.
Sender reputation and email health
- Consistent SPF pass results strengthen sender reputation and aid reputation monitoring across blacklists.
- A routine SPF record lookup with a record checker (e.g., MxToolBox SuperTool) and an SPF raw checker helps catch errors before they impact delivery.
- Platforms such as EasyDMARC’s Delivery Center act as a deliverability platform and diagnostics console, correlating SPF, DKIM, and DMARC outcomes to guide remediation.
How SPF works: DNS TXT records, mechanisms (ip4/ip6/a/mx/include/exists/redirect), and qualifiers (+/−/~/?)
Anatomy of an SPF record in DNS
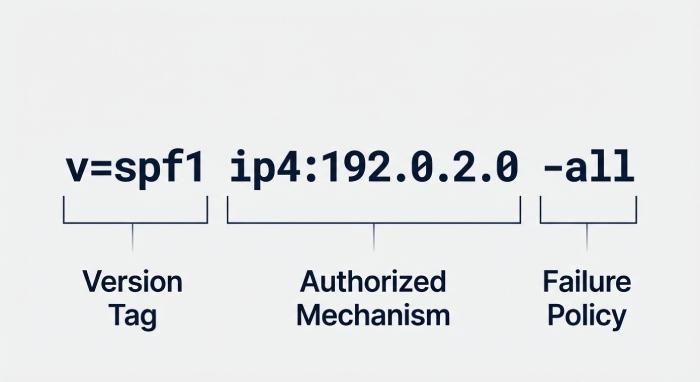
An SPF record is a TXT record published at your domain name (for example, TXT record at example.com). It follows SPF specifications and SPF syntax like: v=spf1 ip4:192.0.2.0/24 ip6:2001:db8::/32 a mx include:_spf.vendor.com -all. Receivers retrieve this DNS data, then evaluate it during SMTP. Key building blocks include:
- ip4 and ip6 mechanisms for authorized IPv4 and IPv6 ranges
- a to reference the domain’s A record
- mx to reference the domain’s MX record set
- include to import third‑party sender definitions
- exists and redirect for advanced delegation and policy design
Because many services send on your behalf, proper SPF record embed decisions (what to place in the TXT record) are crucial to reflect reality across all subdomains.
TXT, A, MX, IPv4/IPv6 and DNS basics
- TXT record: The only supported SPF record type as per current practice; publish a single authoritative TXT record.
- A record and MX record: Let you authorize senders indirectly via hostnames; receivers resolve them over DNS.
- IPv4 and IPv6: Always confirm the exact IPv4 and IPv6 blocks your providers use before you generate SPF record entries.
- DNS: Keep TTLs reasonable; coordinate with your DNS Provider so changes propagate quickly.
Mechanisms and qualifiers in SPF syntax
Mechanisms determine authorization; qualifiers determine the outcome when a mechanism matches. Common mechanisms you will include:
- ip4, ip6, a, mx: Direct or indirect authorization
- include: References a vendor’s SPF record so you don’t list every IPv4/IPv6 yourself
- exists: Tests for the presence of a host; useful for dynamic sources
- redirect: Forwards evaluation to another domain’s SPF record (often used for subdomain policies)
Qualifiers:
- + (pass) is implied; often omitted in practical SPF syntax
- − (fail) produces a hard fail per your failure policy
- ~ (softfail) indicates suspect mail; often used during rollout
- ? (neutral or none-equivalent) means no assertion
include, exists, redirect and failure policy outcomes
- Use include to integrate SaaS senders like EasySender or EasySPF safely.
- exists can solve edge cases when IPs are not static.
- redirect helps consolidate policies under one domain name, especially for subdomains.
- Choose a failure policy based on risk tolerance: -all (fail), ~all (softfail), ?all (neutral/none). Move from softfail to fail once you confirm a valid SPF record via repeat SPF record check cycles and an email header analyzer.
SPF, DKIM, and DMARC: alignment, policy, and why SPF alone isn’t enough
Alignment and policy across authentication protocols
SPF should be deployed with DKIM and DMARC to form layered authentication protocols. DMARC requires identifier alignment: either SPF’s domain name (envelope-from/Return-Path) aligns with the visible From, or DKIM d= aligns. Because SPF can break on forwarding, DKIM often preserves alignment; DMARC then enforces policy (monitor, quarantine, reject) and reports outcomes for diagnostics. Complementary controls BIMI for brand indicators, MTA-STS and TLS-RPT for transport security round out email security.
Reviews on G2 Crowd, SourceForge, and Expert Insights can help you compare SPF tools, DMARC analyzers, and delivery platforms. Vendors like EasyDMARC (with EasyDMARC Academy training, Delivery Center analytics, and an MSP Program for msps) and community resources showcased at RSAC or through a Channel Program often cover end-to-end guidance, from DNS record checker utilities to alert manager workflows and domain scanner capabilities.
What an SPF generator does: automate vendor includes, prevent errors, and manage complexity
Automate includes and avoid errors
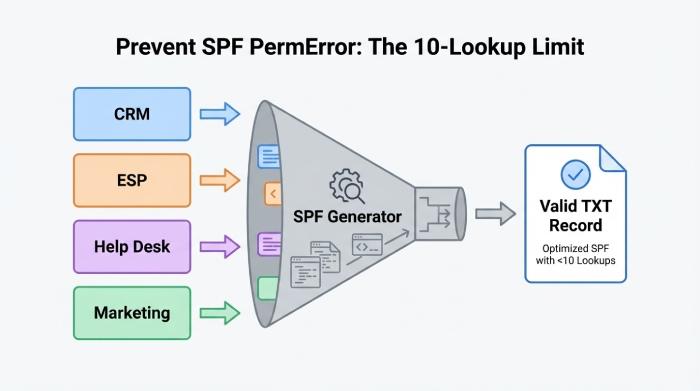
An SPF generator streamlines complex SPF policies by:
- Normalizing provider details into precise ip4/ip6 entries or an include statement that a receiver can validate.
- Enforcing SPF specifications such as the 10‑DNS‑lookup limit to avoid permerror.
- Acting as a record analyzer, record generator, and record validator to ensure a valid SPF record before publishing.
- Providing an SPF record check and record found confirmation, often with a DNS record checker integration.
- Offering a record checker to simulate results, a domain scanner to find stray senders, and an alert manager for changes.
- Supporting managed SPF approaches so you rarely need a risky manual edit to modify SPF record entries.
Well-designed SPF tools also export configurations for your DNS Provider and guide you to generate SPF record content that’s copy‑safe for a TXT record. Many include a SPF record creator wizard, a SPF record generator mode for bulk domains, and a SPF raw checker for power users.
Popular utilities like MxToolBox and its SuperTool, as well as EasyDMARC’s Delivery Center, provide SPF record lookup, record analyzer views, and ongoing reputation monitoring. Some suites brand modules as EasySPF or EasySender to simplify vendor onboarding.
Preparing inputs: inventory all senders and subdomains
Before you generate SPF record entries, audit every system that can send with your domain name:
- ESPs and marketing automation powering email campaigns
- CRM and sales engagement tools
- Ticketing systems and help desk platforms
- Security scanners, monitoring, and Bettertracker‑style reports
- Web apps, web servers, and transactional MTAs
Engage your IT and marketing teams to gather IPv4/IPv6 details, hostnames for A record/MX record‑based relays, and the vendor’s published target. Use an email header analyzer on recent messages to confirm Return‑Path domains. Capture subdomain use (e.g., alerts.domain.com) and decide if you’ll use redirect to a central policy or bespoke SPF policies per subdomain. Document current email configuration and any deliverability platform dependencies to avoid regressions when you modify SPF record parameters.
Common sources: ESPs, CRM, ticketing, scanners, web apps
- For each vendor, confirm whether they provide an include record or require explicit ip4/ip6 entries.
- Validate with a DNS record checker that the include chain is healthy and won’t exceed the 10‑lookup limit.
- Run SPF record lookup tests in staging, then production, and monitor softfail/fail/neutral/none outcomes with DMARC reports and mailbox tests.
Checklist before you generate SPF record
- List every sending host by domain name, IPv4, and IPv6.
- Note whether authorization will come via A record, MX record, ip4/ip6, include, exists, or redirect.
- Verify vendor docs against live DNS using a record checker and SPF checker.
- Publish to DNS as a single TXT record; avoid duplicates.
- Re‑test with an email header analyzer and mail-flow diagnostics.
- Track results with Delivery Center dashboards; escalate anomalies to your MSP Program partner if using msps.
Finally, keep iterating: as services change, promptly modify SPF record content, re‑run an SPF record check, and confirm “record found” results. This ongoing discipline paired with DMARC, DKIM, and reputation monitoring sustains email deliverability, strengthens email security, and protects your brand’s domain name at scale.
Step-by-step: Using an SPF Generator to Build a Robust Record
Inventory your sending sources and DNS dependencies
Start by mapping every system that sends mail for your domain name. Include your primary MTA, marketing platforms, CRM triggers, ticketing systems, ERP alerts, and any MSPs providing outbound email security. Document each sender’s IPv4 and IPv6 ranges, the hostnames they use, and whether they want you to reference an MX record, an A record, or an include they publish (for example, include:_spf.vendor.com). This inventory underpins both email security and email deliverability.
- Confirm actual envelope-from/Return-Path domains used by your email campaigns.
- Capture host-to-IP mappings to decide whether to authorize via ip4, ip6, a, or mx mechanisms.
- Note subdomain use; each fully qualified domain name may need its own policy.
- Verify that each third-party deliverability platform provides a supported include and adheres to SPF specifications.
Finally, confirm your DNS hosting and update process with your DNS Provider, including who can manually edit a TXT record and how changes propagate.
Build your policy with a reliable SPF record generator
Using an SPF generator reduces syntax errors and helps you generate SPF record outputs that respect the 10-lookup rule. A reputable SPF record generator or SPF record creator will prompt you to add IPv4 and IPv6 ranges, include vendor directives, and decide on a failure policy (-all for fail, ~all for softfail, ?all for neutral, +all for none). If you need a tool, try the SPF generator.
Example outputs: choosing -all vs ~all
Example 1 (strict production stance, fail unknown senders):
TXT record:
v=spf1 ip4:203.0.113.0/24 ip6:2001:db8::/32 a mx include:_spf.mailvendor.com -all
Example 2 (transitional stance during rollout, softfail unknown senders):
TXT record:
v=spf1 a mx include:spf.mailvendor.com include:spf.send.example.com ip4:198.51.100.40 ~all
Use ~all while you audit, then modify SPF record to -all when you’re confident no legitimate sources are missing. This two-phase approach protects inbox placement and sender reputation while you iterate.
Mechanism choices and SPF syntax tips
- Use a for hosts with a stable A record, mx if you rely on your MX record for sending, and ip4/ip6 to explicitly cover IPv4/IPv6 networks.
- Prefer include for third-party vendors; it keeps your TXT record readable and defers IP maintenance to the vendor.
- Keep SPF syntax minimal: mechanisms first, then qualifiers (+ default, ~ softfail, – fail, ? neutral). Ensure you produce a valid SPF record that terminates with an explicit policy.
Key Takeaways
- Use a trustworthy SPF record generator to generate SPF record outputs, validate SPF syntax, and stay within the 10-lookup limit.
- Prefer include for vendors, avoid multiple SPF records, and publish one concise TXT record with explicit IPv4/IPv6 where practical.
- Validate with dig/nslookup and reputable SPF checker tools, then confirm SPF=pass via an email header analyzer in real test messages.
- Monitor with DMARC, automate updates, and apply version control to maintain email health, sender reputation, and inbox placement over time.